FTC Issues Health Breach Notification Policy Statement
G7 Ministers issue tech and online commitments; U.S.-EU Trade and Technology Council meeting announced; EU Export Control Regulation comes into force
Photo by Onur Binay on Unsplash
The Federal Trade Commission (FTC) held two meetings last week at which the three Democratic Commissioners continued to lay the groundwork for aggressive future action against a number of large companies and the technology field. Today, I will cover one of the items at the open meeting and will address the others tomorrow.
At an open meeting, the FTC debated and then took a number of actions as explained in their press release:
§ Proposed Policy Statement on Privacy Breaches by Health Apps and Connected Devices: The Commission voted to issue a policy statement on the importance of protecting the public from privacy breaches by health apps and other connected devices.
§ Non-HSR Reported Acquisitions by Select Technology Platforms, 2010-2019: An FTC Study: Staff presented some findings from the Commission’s inquiry into large technology platforms’ unreported acquisitions, including an analysis of the structure of deals that customarily fly under enforcers’ radar.
§ Proposed Revisions to FTC Procedural Rules Concerning Petitions for Rulemaking: The Commission voted on putting in place a process to receive public input on rulemaking petitions by external stakeholders.
§ Proposed Withdrawal of 2020 Vertical Merger Guidelines: The Commission voted on whether to rescind the Vertical Merger Guidelines adopted in June 2020 and the Commentary on Vertical Merger Enforcement issued in December 2020.
As mentioned, I will only address the FTC’s policy statement on privacy breaches by health apps and connected devices. Basically, this policy statement would cover breaches involving healthcare information that fall outside the Health Insurance Portability and Accountability Act of 1996 (HIPAA)/Health Information Technology for Economic and Clinical Health (HITECH) Act rules, and this basically means all non-healthcare providers. So, think FitBit, Strava, and other companies looking to move into healthcare data that are not healthcare providers. In 2020, the FTC asked for input on its Health Breach Notification Rule (HBN Rule) that promulgated in 2010 per direction in the “American Recovery and Reinvestment Act” (ARRA) (P.L. 111-5) (see here for more detail and analysis.) In 2016 the agency posted on its website a page titled “Mobile Health App Developers: FTC Best Practices” with detailed advice for these entities in how to adhere to U.S. law.
The FTC is not the only governmental entity that has noticed the proliferating market for healthcare data. A bill (AB-1436 “Information privacy: digital health feedback systems”) to tighten California’s laws regarding the collection and use of health information by non-healthcare providers passed the Assembly but stalled in the Senate. A summary of the legislation explained:
§ Certain information and transactions, however, are expressly exempt from the California Consumer Privacy Act of 2018 (CCPA). As related to health care, the CCPA does not apply to the following:
o Medical information governed by the Confidentiality of Medical Information Act (CMIA) or protected health information (PHI) that is collected by a “covered entity” or “business associate,” as defined and governed by the privacy, security, and breach notification rules under HIPAA and the Health Information Technology for Economic and Clinical Health Act (HITECH).
o A provider of health governed by the CMIA or a covered entity governed by HIPAA.
o Information collected as part of a clinical trial subject to the Federal Policy for the Protection of Human Subjects (Common Rule), pursuant to good clinical practice guidelines issued by the International Council for Harmonisation, or human subject protection requirements of the U.S. Food and Drug Administration.
The bill’s sponsor, Assemblyman Ed Chau (D), explained the problem the bill is designed to solve:
These tech companies are after all sorts of personal medical information — your heart rate, your blood pressure, your sleep habit. As it stands, they’re circumventing medical privacy laws.
It bears some emphasis that the FTC’s action is not a new rule or regulation. Rather, it is a policy statement. According to long accepted administrative law doctrine, policy statements are agency pronouncements on “substantive law or policy, of general or particular applicability and future effect, that was not issued legislatively (i.e., not a regulation) and is not an interpretive rule (i.e., not an agency interpretation of a statute.)”[1] Hence, many FTC policy statements are, in a sense, a warning of how the agency intends to use its discretionary enforcement powers, and this is a tool the FTC under new Chair Lina Khan has been using more and more to put certain companies and entities on notice about likely future uses of its Section 5 powers against unfair and deceptive practices.
Turning to the policy statement itself, the FTC stated:
There is a lot here. The FTC has never even enforced the Health Breach Notification Rule after promulgating it over ten years ago, and now the agency is putting on notice those “health care providers” (a term that does not mean HIPAA/HITECH regulated entities) that collect, process, use, and share “personal health records” with “identifiable health information.” This rule, however, only covers breaches and does not impose security or privacy requirements on health care providers in the same way the HIPAA/HITECH regulations do. Incidentally, because of how Congress drafted the language, violators of the Health Breach Notification Rule can be fined up to almost $44,000 per incident (which could be the breach of every person’s records) even for first violations.
The FTC’s policy statement explicitly pulls apps into the ambit of the rule because the regulations define “personal health record[s]” an electronic record of PHR identifiable health information on an individual that can be drawn from multiple sources and that is managed, shared, and controlled by or primarily for the individual.” The FTC reads this to include those apps that people share their health data with and that can acquire their information such as heart rate, steps walked, etc. The FTC added that even those apps that draw information on people from more than one source are covered, and hence, an app that measures heart rate and also accessed location data would qualify.
In her statement of support of the policy statement, Khan asserted:
In his dissent, Commissioner Noah Joshua Phillips objects on two procedural grounds. First, the FTC has not finished its aforementioned process of assessing its Health Breach Notification Rule. Second, the Department of Health and Human Services (HHS) is conducting a HIPAA/HITECH rulemaking of its own that will likely encompass health apps.
In his statement, Commissioner Rohit Chopra addresses both of Phillips arguments:
Additionally, if one references the FTC’s Federal Register notice on the Health Breach Notification Rule, one finds this explanation:
And so, the FTC is not conducting a rulemaking, The notice does not obligate the agency to act, nor is the agency acting inappropriately in issuing a policy statement, for there is no rulemaking procedure, the procedural limits of which the agency would be bound to follow.
However, Phillips really goes after the majority regarding the implications of the policy statement:
The pertinent section of ARRA reads:
each vendor of personal health records, following the discovery of a breach of security of unsecured PHR identifiable health information that is in a personal health record maintained or offered by such vendor, and each entity described in clause (ii), (iii), or (iv) of section 13424(b)(1)(A), following the discovery of a breach of security of such information that is obtained through a product or service provided by such entity, shall-
(1) notify each individual who is a citizen or resident of the United States whose unsecured PHR identifiable health information was acquired by an unauthorized person as a result of such a breach of security; and
(2) notify the Federal Trade Commission.
Section 13424(b)(1)(A) lists the other entities that must also report breaches of security for unsecured PHR identifiable health information:
(ii) entities that offer products or services through the website of a vendor of personal health records;
(iii) entities that are not covered entities and that offer products or services through the websites of covered entities that offer individuals personal health records;
(iv) entities that are not covered entities and that access information in a personal health record or send information to a personal health record;
The majority is likely hanging its policy statement on the entities described in clause (iv), that is non-HIPAA/HITECH regulated entities that access or send information in PHRs. Were it not for the reference to this extra class of entities, Phillips assertion that only health records vendors are covered would be stronger.
Moreover, Phillips implicit claim that the FTC owns some sort of deference to or should operate out of comity with other agencies with overlapping jurisdiction is far from settled law. Absent a statutory mandate, agencies do not have to coordinate with others even if they are regulating or acting in the same space. Whether that is wise or not is another matter, but the FTC need not heed other agencies’ interpretations.
Finally, the majority may well agree that Phillips is right about the possible scope of the Health Breach Notification rule and the current landscape today. By all accounts, companies are engaged in a landgrab of personal data, some of which is identifiable health information, and so, Phillips may well be right in terms of which entities could fall into this rule. Khan, Slaughter, and Chopra would seem to agree on this point and think people need to be protected in the event these entities handle their personal data in ways that lead to a breach.
Phillips then accuses the majority of conflating (perhaps purposefully so) breaches with “privacy misrepresentations,” and by this objection he means principally the claim that a disclosure of “sensitive health information without users’ authorization, this is a “breach of security” under the Rule.” Here is the relevant excerpt:
In the Subtitle of ARRA that directs the FTC to promulgate the Health Breach Notification Rule, Congress defined breach this way:
the unauthorized acquisition, access, use, or disclosure of protected health information which compromises the security or privacy of such information, except where an unauthorized person to whom such information is disclosed would not reasonably have been able to retain such information.
However, a more specialized definition seems to control here: “Breach of security:”
with respect to unsecured PHR identifiable health information of an individual in a personal health record, acquisition of such information without the authorization of the individual.
Phillips claims to be confused by the majority’s formulation of when a breach occurs in a situation where a covered entity shares covered personal data without authorization from the person. He seems to ask if the covered entity should then report a breach when it draws up its plans to share people’s data or after the information is shared. Phillips then adduces how privacy regulations usually work in that violations are clearly defined and prohibited. He concludes by claiming the way the majority’s policy statement would work turns the usual paradigm on its head and covered entities could still share the information after discovery of the breach.
Real or perceived snark aside, it would seem the majority is indeed trying to backdoor the requirement that health app operators obtain a person’s authorization before her identifiable health information could be shared. However, in the context of this rule, it appears that a breach of security is a breach of security regardless of whether it is nefarious hackers in Russia obtaining the information or the company itself not meeting its duty not to allow the “acquisition of such information without the authorization of the individual.” Therefore, should a health app share covered information without a person’s authorization, then a breach of security has occurred. Consequently, the logical outcome is that health apps would seek authorization from people before sharing or face enforcement by the FTC.
If he is to be taken seriously, Phillips elides the ramifications of breach notification (i.e., fines of nearly $44,000 per violation), and one could see the current FTC pushing for higher fines given the willful nature of the conduct if an entity knowingly allows for the unauthorized access of personal data through sharing with a third party.
Commissioner Christine S. Wilson makes some of the same points as Phillips with respect to issuing a policy statement during a rulemaking and failing to coordinate with HHS and other agencies to harmonize the FTC’s new approach. Notably, Wilson claims the FTC’s new policy statement conflicts with existing guidance on this issue:
Assuming this presents an issue, presumably the FTC could merely announce the withdrawal of the guidance and inform entities to heed the policy statement.
Commissioner Rebecca Kelly Slaughter discussed the limits of policy statements and urged the agency to conduct a rulemaking to require entities to better secure health information:
Slaughter may be calling for Congress to pass a privacy law and/or for the agency to conduct a rulemaking on privacy. It is not exactly clear which.
Other Developments
Photo by Luke Stackpoole on Unsplash
§ Following a three day meeting, the G7 Interior and Security Ministers published their “Ministerial Commitments” that explained “the G7 Interior and Security Ministers and senior officials, along with representatives from the European Union and the Secretary General of INTERPOL.” The G7 issued annexes in conjunction with the ministerial commitments: “G7 London Interior Commitments Annex 1: Statement on Preventing Terrorism Online” and “G7 London Interior Commitments Annex 2: Protecting Against Online Exploitation Violence and Abuse” Here are relevant excerpts from the G7 meeting’s commitments:”
§ The White House announced a 29 September meeting of the U.S.-EU Trade and Technology Council (TTC), a body created in June 2021, established “to expand and deepen trade and transatlantic investment ties and update the rules of the road for the 21st century economy.” The Biden Administration explained:
o President Biden’s delegated co-chairs for the TTC, Secretary of State Antony Blinken, Secretary of Commerce Gina Raimondo, and United States Trade Representative Katherine Tai, will host European Commission Executive Vice Presidents Margrethe Vestager and Valdis Dombrovskis for the inaugural TTC meeting on September 29th in Pittsburgh, Pennsylvania.
o The TTC’s ten working groups will tackle a diverse set of challenges, including technology standards cooperation, supply chain security, climate and green technology, ICT security and competitiveness, data governance and technology platforms, the misuse of technology threatening security and human rights, export controls, investment screening, global trade challenges, and access to, and use of, digital technologies by small and medium enterprises. In conjunction with the TTC, both governments are committed to robust and ongoing engagement with a broad range of stakeholders to ensure that the outcomes from this cooperation support broad-based growth in both economies and are consistent with our shared values.
§ There was also a “Roundtable Of G7 Data Protection And Privacy Authorities” the United Kingdom’s (UK) Information Commissioner’s Office (ICO) hosted and chaired. The G7 data privacy and protection authorities discussed the following issues and made commitments for future work in these areas:
o Privacy and Competition Intersection – Cross-Regulatory Collaboration to Support a Robust Global Digital Economy
o Shaping the Future of Online Tracking
o Designing Artificial Intelligence in line with Data Protection
o Redesigning Remedies for the Digital Age
o Pandemic-Driven Tech Innovation: A Stress Test for Data Protection Rights
o Government Access and Data Flow at International Level: What Role for Regulatory Cooperation in Ensuring Real Trust?
o Development of a Framework for Cross-Border Transfer of Personal Data and Cooperation between G7 Data Protection Authorities
§ The European Commission (EC) lauded the new Export Control Regulation in taking effect that “will tighten controls on trade in dual-use items – civilian goods and technologies with possible military or security use – while enhancing the EU’s capacity to protect human rights and support secure supply chains for strategic items.” The EC asserted:
o The new framework allows the EU to take a number of important actions to pool expertise and tackle particular challenges, notably in relation to cyber-surveillance – where due diligence guidelines are in preparation – but also emerging dual-use technologies such as advanced computing.
o The regulation introduces greater transparency by increasing the level of consultations and reporting between Member States and the Commission, contributing to the development of a new EU electronic licensing platform already piloted in four EU Member States.
o It also provides a legal basis for EU action at multilateral, plurilateral and bilateral levels – recognising that the effectiveness of controls depends on the cooperation of the main technology producers – and builds on the existing multilateral framework of export controls, namely the Wassenaar Arrangement, which forms the basis for many restrictions imposed by the regulation at EU level.
§ Illinois Governor JB Pritzker signed into law the “Protecting Household Privacy Act” (HB 2553) that “[p]rohibits law enforcement agencies from obtaining household electronic data from a private third party unless the agency has a warrant or meets other specific exceptions” according to a summary from the Governor’s office.
§ Outgoing Information Commissioner Elizabeth Denham gave a speech in which she argued the world “need[s] a data Bretton Woods.” She asserted:
o Our digital world is international. Data flows around the world in a heartbeat. I open up my phone, check an app, and in a moment my data travels around the globe. Services like geolocation and cloud computing all rely on international data flows.
o But the checks and balances on this data are domestic.
o That brings problems.
o It means that when a multinational company doesn’t follow the rules, or when there is an international data breach, the ability for regulators to work together across jurisdictions can be limited, as we try to match up our differing legal systems and approaches.
o It means that there are companies who develop apps available to people in the UK, but based in jurisdictions with little or no data protection provisions
o And it means that our system for international data flows is based on assessments of how other nations’ laws measure up to our own, no matter how many flaws we may be willing to acknowledge in our own systems.
o It is my view that a Bretton Woods conference for data is required today.
o It is accepted that the digital world is borderless.
o It is accepted that the flow of data, from individual to organisation, from organisation to organisation, from country to country, is integral to digital innovation.
o It is accepted – I hope – that such data flows rely on the public trust earned through sensible data protection regulation.
o And yet we continue to consider those protections domestically. That needs to change.
o Let’s be clear from the outset: this is not about creating a global law that everyone must follow. It is not about deciding there is only one law to rule them all.
o A Bretton Woods conference could provide the melting pot of ideas needed to take this forward.
o It could consider how best to provide that plumbing.
o My own view is that a global data protection accord could find common ground between nation’s data protection regimes.
o Membership would rely on countries demonstrating their commitment to data protection, backed by independent regulation. And organisations within those member nations would be able to transfer low risk data to countries who were fellow members.
o Crucially, the bar for membership would be lower than adequacy. Membership of a global data protection accord would not require countries to demonstrate their law offered the same safeguards as, say, the GDPR.
o Businesses would benefit from the surety of a system less vulnerable to legal challenge, and much broader than partnerships with individual nations.
o And consumers would know that simple protections are in place for their data around the globe.
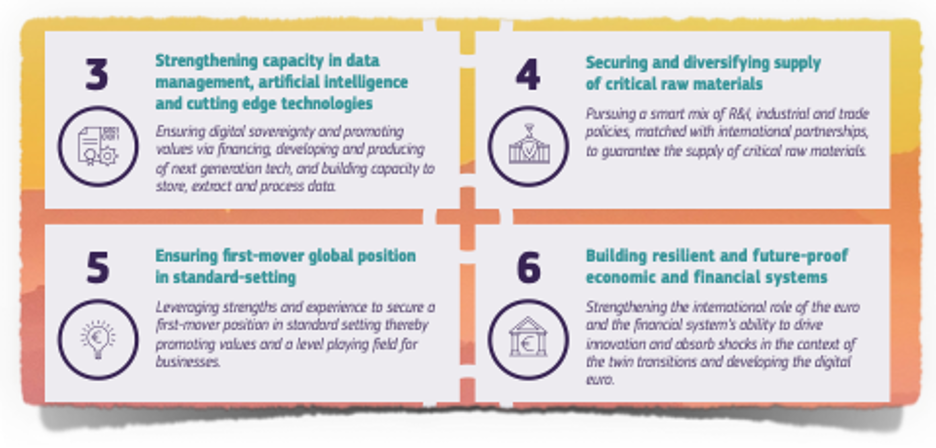
§ The European Commission (EC) published its “2021 Strategic Foresight Report” that “presents a forward-looking and multi-disciplinary perspective on the EU’s capacity and freedom to act in the coming decades.” This document was issued in conjunction with the Joint Research Centre (JRC)’s “Shaping and securing the EU's Open Strategic Autonomy by 2040 and beyond.” In the “reader-friendly” version, the EC provided a visualization of the problems it sees coming:
o The EC further explained “Digital hyperconnectivity and technological transformations:”
§ To be technologically and digitally sovereign, the EU will need to support the development and uptake of human-centred knowledge and technologies. The EU is a strong player in terms of knowledge and innovation: it accounts for almost 20% of the world’s total research and development, publications and patenting activity. However, it lags behind global competitors in private investment into research and other indicators. The EU has a performance gap with Australia, Canada, Japan, South Korea and the United States. Since 2014, its position improved to Australia, Canada, Brazil, India, Russia and South Africa but worsened to Japan, South Korea, the USA and China.
§ Despite the uncertainty accompanying emerging technologies, it is clear that a number of breakthrough innovations can be key for the twin transitions and competitiveness. The EU is a technological champion in advanced manufacturing and materials, with its firms delivering many critical enablers to global production lines. It is a leader in future smart and sustainable mobility and low-carbon technologies. The EU’s capabilities in artificial intelligence, big data and robotics are similar to Japan’s, but it needs to catch up with leaders: the USA and China. In key quantum technologies, the USA, Japan and China are currently in the lead. By 2025, the EU will have its first computer with quantum acceleration and if matched with investment, it could be at the cutting edge of quantum capabilities by 2030.
§ Other promising technologies include microelectronics, new materials for bio-degradable electronics, flexible and printed electronics, and 2D material based technologies such as graphene. Moreover, many pilot technologies have high decarbonisation potential. These include clean hydrogen, low carbon fuels, carbon capture and storage/usage, next-generation sustainable batteries, bio-based technologies and materials, methane cracking, high temperature superconductivity, advanced geothermal and ocean energy, high altitude wind energy generation, and advanced fusion-based nuclear reactors. Various nature-based solutions, like large-scale reforestation also have major potential in this context.
§ Beyond specific technologies, hyperconnectivity is driving the transformation. It results in an increased convergence of industries, products, technologies and services. The number of connected devices globally might increase from 30.4 billion in 2020 to 200 billion in 2030. Increased connectivity of objects, places and people will result in new products, services, business models, life and work patterns. At the same time, it results in the increased risk of cyber-attacks and network outages, in both digital and physical world, e.g. essential infrastructures like pipelines and hospitals. It might also increase the threat of intellectual property and data loss and theft. Hyperconnectivity has only accelerated with the pandemic and its social impact needs to be carefully monitored.
§ However, new technologies and hyperconnectivity do not come without challenges. Certain jobs will be lost with automation. Just in the EU in 2018, about 14% of adult workers were found to face a very high risks of automation. In the future, 50% of current jobs globally could be automated, with significant differences across countries and sectors. New jobs will appear, but will require new skills. If left unaddressed, these trends might lead to the erosion of fundamental social rights, and increased inequalities and dependencies within and between states. Moreover, digital transition can increase e-waste, and drive demands for energy or use of rare resources.
o The EC stated it will pursue these strategies:
§ The leadership of the House Homeland Security Committee “introduced the “CISA Leadership Act” (H.R.5186)…[that] would codify the Cybersecurity and Infrastructure Security Agency (CISA) Director’s tenure as a 5-year term and reaffirm that the position will be Presidentially appointed, and Senate confirmed.”
§ The Irish Council for Civil Liberties (ICCL) published a report on the European Union’s data protection authorities regarding enforcement of the General Data Protection Regulation (GDPR). The ICCL offered these key insights from the report titled “Europe’s enforcement paralysis”:
o The Irish Data Protection Commission is the bottleneck of GDPR enforcement against Big Tech across the EU. Almost all (98%) major GDPR cases referred to Ireland remain unresolved.
o Though Covid-19 has forced many Europeans to work online, DPAs remain ill equipped to supervise the tech sector. Only 9.7% of EU DPAs 2,950 full time staff are tech specialists.
o Less than half (44%) of EDPB final EU-wide decisions include corrective measures, such has fines or orders to stop processing.
o A small number of Member States (Ireland, Spain, Germany, Netherlands, France, Sweden, and Luxembourg) receive almost three quarters (72%) of all cross-border complaints referred between DPAs.
o EU countries’ investment in DPAs is declining.
o Germany alone accounts for almost a third (32%) of all spending on EU DPAs that oversee the private sector. More than half of all national DPAs have small (€5 million or less) annual budgets.
o The ICCL offered these recommendations:
§ Recommendation 1
· The Irish Data Protection Commission (DPC) must be reformed and strengthened. The recommendations of the Justice Committee of the Irish Parliament and Senate2 should be urgently implemented. In particular:
· The Irish Government should provide for an independent review of how to strengthen and reform the DPC. This is necessary to fulfil Ireland’s duty of sincere cooperation under Article 4(3) of the Treaty on European Union (TEU), and to fulfil its duties under Article 52(4) of the GDPR.
· The Irish Minister for Justice should user her power to appoint two additional Data Protection Commissioners.
· The DPC must “move from emphasising guidance to emphasising enforcement as a matter of urgency”.
§ Recommendation 2
· The European Commission should use its power under Article 258 of the Treaty on the Functioning of the European Union to launch an infringement procedure against Member States that jeopardise the protection of personal data. Data protection is one of the Union’s objectives. Jeopardising it is a failure to fulfil Member States’ obligations under Article 4(3) of the TEU.
§ Recommendation 3
· The European Commission must improve its monitoring of the application of the GDPR. It should request that the EDPB and DPAs publish the following data each quarter in order to enable it to perform its duty under Article 17 of the TEU:
· Time (days) to progress each case from first complaint or proactive investigation to draft decision and then to final decision.
· How many cases each DPA is the Lead Supervisory Authority (LSA) for. This should also specify the number of separate cases or complaints combined in each cases.
· How many times each LSA used each investigative power provided in GDPR Article 58(1), in that quarter.
· How many times each LSA used each sanctioning power provided in GDPR Article 58(2), in that quarter.
§ Ireland’s Data Protection Commission (DPC) “commenced two own-volition inquiries pursuant to section 110 of the Data Protection Act 2018 in relation to TikTok Technology Limited’s (TikTok) compliance with requirements of the GDPR.” The DPC provided this detail:
o The first inquiry will examine TikTok’s compliance with the GDPR’s data protection by design and default requirements as they relate to the processing of personal data in the context of platform settings for users under age 18 and age verification measures for persons under 13. This inquiry will also examine whether TikTok has complied with the GDPR’s transparency obligations in the context of the processing of personal data of users under age 18.
o The second inquiry will focus on transfers by Tiktok of personal data to China and TikTok’s compliance with the GDPR’s requirements for transfers of personal data to third countries.
§ The United States (U.S.) Financial Industry Regulatory Authority (FINRA), a government-authorized not-for-profit organization that oversees U.S. broker-dealers. issued a report “Cloud Computing in the Securities Industry” and request for comments. FINRA claimed “During discussions with market participants, several common themes emerged:
o The use of Software as a Service (SaaS) products was prevalent. Many firms, particularly smaller firms, used off-the-shelf SaaS cloud products for non-core business functions, such as email systems, customer relationship management, financial accounting and human resources operations.
o Roll-outs of cloud infrastructure tended to be targeted, incremental and iterative. The majority of firms took a measured approach instead of launching a wholesale migration of the business to the cloud, acknowledging the need for project modifications, specialized skills and training, and measuring financial impact.
o Firms focused heavily on governance, cloud security and training. Firms noted it was important to develop governance and cloud security policies and procedures to safeguard data and systems, often leveraging enhanced security protocols in the cloud environment.
o Organization and cultural changes often accompanied cloud adoption. Optimizing cloud capabilities required changes in the way people work-ensuring greater responsiveness to business needs and enhanced time-to-market capabilities. Cloud adoption often coincided with firms' reassessing their areas of technology expertise, frequently with existing staff being re-trained or acquiring new staff with cloud expertise.
Further Reading
Photo by Thought Catalog on Unsplash
§ “Facebook Says Its Rules Apply to All. Company Documents Reveal a Secret Elite That’s Exempt.” By Jeff Horwitz — The Wall Street Journal. Mark Zuckerberg has publicly said Facebook Inc. allows its more than three billion users to speak on equal footing with the elites of politics, culture and journalism, and that its standards of behavior apply to everyone, no matter their status or fame. In private, the company has built a system that has exempted high-profile users from some or all of its rules, according to company documents reviewed by The Wall Street Journal.
§ “Facebook Knows Instagram Is Toxic for Teen Girls, Company Documents Show” By Georgia Wells, Jeff Horwitz, and Deepa Seetharaman — The Wall Street Journal. About a year ago, teenager Anastasia Vlasova started seeing a therapist. She had developed an eating disorder, and had a clear idea of what led to it: her time on Instagram. She joined the platform at 13, and eventually was spending three hours a day entranced by the seemingly perfect lives and bodies of the fitness influencers who posted on the app. “When I went on Instagram, all I saw were images of chiseled bodies, perfect abs and women doing 100 burpees in 10 minutes,” said Ms. Vlasova, now 18, who lives in Reston, Va. Around that time, researchers inside Instagram, which is owned by Facebook Inc., were studying this kind of experience and asking whether it was part of a broader phenomenon. Their findings confirmed some serious problems.
§ “Facebook Tried to Make Its Platform a Healthier Place. It Got Angrier Instead.” By Keach Hagey and Jeff Horwitz — The Wall Street Journal. In the fall of 2018, Jonah Peretti, chief executive of online publisher BuzzFeed, emailed a top official at Facebook Inc. The most divisive content that publishers produced was going viral on the platform, he said, creating an incentive to produce more of it. He pointed to the success of a BuzzFeed post titled “21 Things That Almost All White People are Guilty of Saying,” which received 13,000 shares and 16,000 comments on Facebook, many from people criticizing BuzzFeed for writing it, and arguing with each other about race. Other content the company produced, from news videos to articles on self-care and animals, had trouble breaking through, he said.
§ “Facebook Employees Flag Drug Cartels and Human Traffickers. The Company’s Response Is Weak, Documents Show.” By Justin Scheck, Newley Purnell, and Jeff Horwitz — The Wall Street Journal. In January, a former cop turned Facebook Inc. investigator posted an all-staff memo on the company’s internal message board. It began “Happy 2021 to everyone!!” and then proceeded to detail a new set of what he called “learnings.” The biggest one: A Mexican drug cartel was using Facebook to recruit, train and pay hit men. The behavior was shocking and in clear violation of Facebook’s rules. But the company didn’t stop the cartel from posting on Facebook or Instagram, the company’s photo-sharing site.
§ “How Facebook Hobbled Mark Zuckerberg’s Bid to Get America Vaccinated” By Sam Schechner, Jeff Horwitz, and Emily Glazer — The Wall Street Journal. In mid-March, Mark Zuckerberg used his Facebook page to announce a goal that was both ambitious and personal. He wanted his company to use its formidable resources to push 50 million people toward Covid-19 vaccines. In a post and a press release, the chief executive discussed Facebook Inc.’s initiatives to promote vaccines. He unveiled collaborations with global health organizations. And he touted that his company had “already connected more than 2 billion people to authoritative Covid-19 information.”
§ “EU commissioner calls for urgent action against Pegasus spyware” By Daniel Boffey — The Guardian. The EU must swiftly legislate to further protect the rights of activists, journalists and politicians following the Pegasus spyware scandal, and the perpetrators of illegal tapping must be prosecuted, the bloc’s justice commissioner has told the European parliament. Didier Reynders told MEPs that the European Commission “totally condemned” alleged attempts by national security services to illegally access information on political opponents through their phones.
§ “Panama unveils bill to make Bitcoin legal tender” By Julian Dossett — c/net. In what could be the beginning of a global trend, Panama is exploring a fast follow of El Salvador's official embrace of Bitcoin. The day after El Salvador adopted Bitcoin as legal tender, Panamanian Congressman Gabriel Silva introduced a bill designed to provide "legal, regulatory, and fiscal certainty to the use, holding and issuance of digital value and crypto assets in the Republic of Panama." The bill, entitled "Crypto Law: Making Panama Compatible with the digital economy, blockchain, crypto assets, and the internet," was announced on Twitter by Silva on Wednesday. In his tweet, Silva said that the bill had the potential to create jobs, attract investment and foster greater government transparency.
§ “New CISA director wants to spend less time cleaning up after big hacks, more time preparing for them” By Sean Lyngaas — cyberscoop. U.S. cybersecurity officials have scrambled to respond to one major hacking incident after another over the past nine months, from the alleged Russian intrusions into federal networks using bugged SolarWinds software, to the extortion of Colonial Pipeline, which controls the East Coast’s biggest fuel artery. Jen Easterly, the new director of the U.S. Cybersecurity and Infrastructure Security Agency (CISA), wants to break that cycle, and spend less time putting out fires and more time preparing for incidents in an attempt to reduce their impact. It’s a goal that will draw on Easterly’s experience working on cyber operations for the military, and her time trying to safeguard one of the largest U.S. investment banks from hackers.
§ “EU ‘seeking to turn migrant database into mass surveillance tool’” By Jennifer Rankin — The Guardian. The EU has been accused of planning “a powerful tool for the mass surveillance” of migrants through proposed changes to a fingerprint database for asylum seekers. Campaigners from 31 non-governmental organisations, including Amnesty International and the European Network Against Racism, made the charge in an open letter to the European parliament urging MEPs to rethink plans to overhaul the Eurodac database of asylum seekers’ fingerprints.
§ “The Texas Abortion ‘Whistleblower’ Site Still Can't Find a Host” By Lily Hay Newman — WIRED. Under a recently passed Texas law, private citizens can sue anyone involved in helping a person receive an abortion in the state after the sixth week of pregnancy. In response, an anti-abortion group called Texas Right to Life set up a website designed to collect anonymous information about any alleged infractions. Or, at least, it tried to. So far, no company has been willing to host it. The fate of prolifewhistleblower.com remains uncertain, and its absence from the internet does not negate the Texas law or its impacts. But in recent years, internet infrastructure giants have begun to draw blurry lines around who they're willing to have as customers, a sometimes murky process exemplified by the travails of far-right social media network Parler. In contrast, prolifewhistleblower.com offers a rare example of consensus about what constitutes acceptable behavior online.
§ “Brazil’s President Bans Social Networks From Removing Some Posts” By Jack Nicas — The New York Times. President Jair Bolsonaro of Brazil is temporarily banning social media companies from removing certain content, including his claims that the only way he’ll lose next year’s elections is if the vote is rigged — one of the most significant steps by a democratically elected leader to control what can be said on the internet. The new social media rules, issued this week and effective immediately, appear to be the first time a national government has stopped internet companies from taking down content that violates their rules, according to internet law experts and officials at tech companies. And they come at a precarious moment for Brazil.
Coming Events
Photo by Lee Blanchflower on Unsplash
§ 20 September
o The House Rules Committee will meet to consider the rules for floor consideration of continuing appropriations for FY 2022 and the “National Defense Authorization Act for Fiscal Year 2022” (H.R.4350.)
§ 21 September
o The Senate Homeland Security and Governmental Affairs Committee will hold a hearing titled “Threats to the Homeland: Evaluating the Landscape 20 Years After 9/11” with these witnesses:
§ Secretary of Homeland Security Alejandro N. Mayorkas
§ Federal Bureau of Investigation Director Christopher A. Wray
§ National Counterterrorism Center Director Christine Abizaid
o The House Financial Services Committee’s Task Force on Financial Technology will hold a hearing titled “Preserving the Right of Consumers to Access Personal Financial Data”
o The Senate Banking, Housing, and Urban Affairs Committee will consider the nomination of Alan F. Estevez to be Under Secretary of Commerce for Industry and Security.
o The Senate Judiciary Committee’s Competition Policy, Antitrust, and Consumer Rights Subcommittee will hold a hearing titled “Big Data, Big Questions: Implications for Competition and Consumers.”
§ 22 September
o The House Homeland Security Committee will hold a hearing titled “Threats to the Homeland: Evaluating the Landscape 20 Years After 9/11” with these witnesses:
§ Secretary of Homeland Security Alejandro N. Mayorkas
§ Federal Bureau of Investigation Director Christopher A. Wray
§ National Counterterrorism Center Director Christine Abizaid
§ 23 September
o The United Kingdom’s Joint Select Committee will hold a hearing on the government’s draft “Online Safety Bill.”
o The Senate Homeland Security and Governmental Affairs will hold a hearing titled “National Cybersecurity Strategy: Protection of Federal and Critical Infrastructure Systems,” with these witnesses:
§ National Cyber Director Chris Inglis
§ Cybersecurity and Infrastructure Security Agency Director Jen Easterly
§ Federal Chief Information Security Officer Christopher DeRusha
o The House Judiciary Committee’s Antitrust, Commercial, and Administrative Law Subcommittee will hold a hearing titled “Reviving Competition, Part 4: 21st Century Antitrust Reforms and the American Worker.”
§ 28 September
o The Information Security and Privacy Advisory Board (ISPAB) will hold an open meeting and “The agenda is expected to include the following items:
§ —Board Discussion on Executive Order 14028, Improving the Nation's Cybersecurity (May 12, 2021) deliverables and impacts to date,
§ —Presentation by NIST, the Department of Homeland Security, and the General Services Administration on upcoming work specified in Executive Order 14028,
§ —Presentation by the Office of Management and Budget on Executive Order 14028 directions and memoranda to U.S. Federal Agencies,
§ —Board Discussion on recommendations and issues related to Executive Order 14028.
§ 30 September
o The Federal Communications Commission (FCC) will hold an open meeting with this tentative agenda:
§ Promoting More Resilient Networks. The Commission will consider a Notice of Proposed Rulemaking to examine the Wireless Network Resiliency Cooperative Framework, the FCC’s network outage reporting rules, and strategies to address the effect of power outages on communications networks. (PS Docket Nos. 21-346, 15-80; ET Docket No. 04-35)
§ Reassessing 4.9 GHz Band for Public Safety. The Commission will consider an Order on Reconsideration that would vacate the 2020 Sixth Report and Order, which adopted a state-by-state leasing framework for the 4.9 GHz (4940-4900 MHz) band. The Commission also will consider an Eighth Further Notice of Proposed Rulemaking that would seek comment on a nationwide framework for the 4.9 GHz band, ways to foster greater public safety use, and ways to facilitate compatible non-public safety access to the band. (WP Docket No. 07-100)
§ Authorizing 6 GHz Band Automated Frequency Coordination Systems. The Commission will consider a Public Notice beginning the process for authorizing Automated Frequency Coordination Systems to govern the operation of standard-power devices in the 6 GHz band (5.925-7.125 GHz). (ET Docket No. 21-352)
§ Spectrum Requirements for the Internet of Things. The Commission will consider a Notice of Inquiry seeking comment on current and future spectrum needs to enable better connectivity relating to the Internet of Things (IoT). (ET Docket No. 21-353)
§ Shielding 911 Call Centers from Robocalls. The Commission will consider a Further Notice of Proposed Rulemaking to update the Commission's rules regarding the implementation of the Public Safety Answering Point (PSAP) Do-Not-Call registry in order to protect PSAPs from unwanted robocalls. (CG Docket No. 12-129; PS Docket No. 21-343)
§ Stopping Illegal Robocalls From Entering American Phone Networks. The Commission will consider a Further Notice of Proposed Rulemaking that proposes to impose obligations on gateway providers to help stop illegal robocalls originating abroad from reaching U.S. consumers and businesses. (CG Docket No. 17-59; WC Docket No. 17-97)
§ Supporting Broadband for Tribal Libraries Through E-Rate. The Commission will consider a Notice of Proposed Rulemaking that proposes to update sections 54.500 and 54.501(b)(1) of the Commission’s rules to amend the definition of library and to clarify Tribal libraries are eligible for support through the E-Rate Program. (CC Docket No. 02-6)
§ Strengthening Security Review of Companies with Foreign Ownership. The Commission will consider a Second Report and Order that would adopt Standard Questions – a baseline set of national security and law enforcement questions – that certain applicants with reportable foreign ownership must provide to the Executive Branch prior to or at the same time they file their applications with the Commission, thus expediting the Executive Branch’s review for national security and law enforcement concerns. (IB Docket No. 16-155)
[1] Robert A. Anthony, Interpretive Rules, Policy Statements, Guidances, Manuals, and the Like—Should Federal Agencies Use Them to Bind the Public?, 41 Duke Law Journal 1311-1384 (1992)
Available at: https://scholarship.law.duke.edu/dlj/vol41/iss6/1